While cloud computing has opened up new possibilities for businesses embarking on a digital transformation journey, it is prone to network attacks and identity theft.
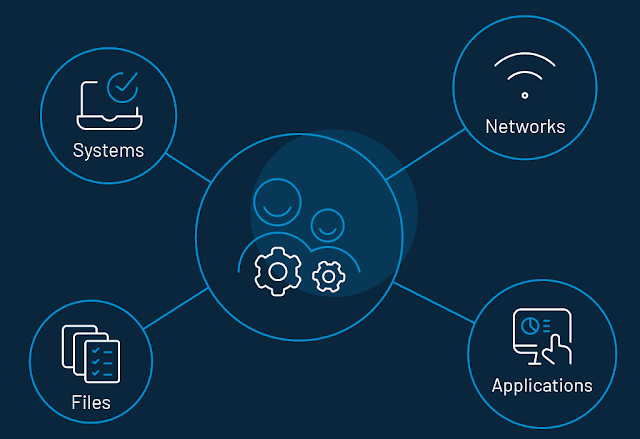
Identity management in cloud computing is primarily concerned with dealing with personal identity information in order to accurately control a user's access to data, computer resources, applications, and services.
A few years ago, business leaders, particularly key decision-makers, were focused on establishing an innovative IT environment that delivered operational agility and competitive advantage as crucial advantages using cloud-based services.
This is where cloud IAM helped in the development of federation capabilities. This decreased the amount of effort required for a single customer, resulting in an innovation wave that helped save costs and hastened integration with other SaaS apps.
Furthermore, businesses that did not use consumer identity and access management providers prior to the global pandemic are now using cloud-based CIAM to assist minimize identity theft and improve access control.
CIAM is a solution that gives you direct control over your customer experience. The most important elements are registration, authentication, account management, consent and preference management, and customer data security.
How Consumer IAM Meets CIO, CMO, CISO Goals
With a variety of job roles, consumer identity management may still match the goals of the CIO, CMO, and CISO. Are you curious as to how? Here are five ideas:
- Enables Secure Access
- Scalability and Speed
- Prioritizes Security Risks
- Complies with Privacy Regulations
- Improves Consumer Experience
A consumer identity management platform has all of the features necessary to completely transform the consumer experience. They also result in increased income and reduced acquisition costs.
For example, CIAM encourages customers to try all of the company's digital offerings by providing a smooth login experience. This allows consumers to become more engaged in a digital area without exerting more effort.
LoginRadius’ Approach to Cloud IAM
LoginRadius is a streamlined consumer identity and access management (CIAM) solution that assists major company stakeholders in driving automation, authentication, effective compliance, and other requirements.
CIOs, CISOs, and CMOs can manage identities on the go while operating complex ecosystems with the cutting-edge consumer identity management platform. The following are some of the features:
- Authentication
- Authorization
- Security Compliance
- Optimized Data Collection
- Unified view of Consumers
- Advanced Login Options
Cloud IAM is paving the way for more robust and secure cloud deployments that protect customer identities while also assisting in the delivery of a flawless user experience.
When a cybercrime occurs, it takes much more than simply customer data. When a business experiences a security breach, everything is on the line, from finances to brand reputation.
To mitigate the architectural complexities that cybercriminals prey on, CIOs, CSOs, and CISOs must all work together.
Comments
Post a Comment